Online Tracker 4846017041 Prism Pulse
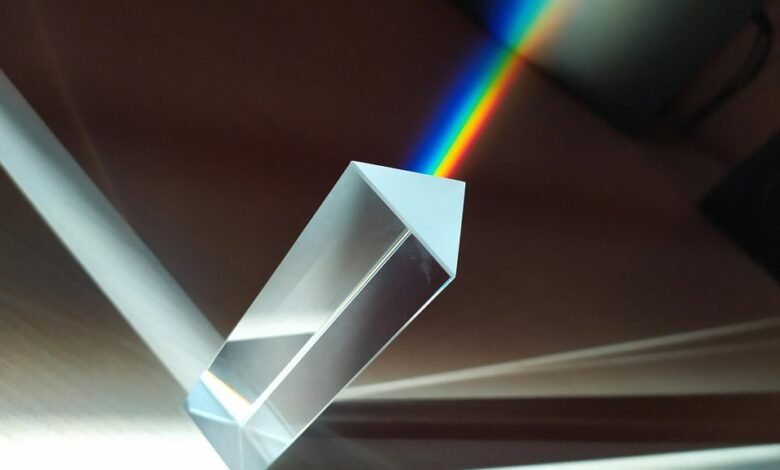
Prism Pulse 4846017041 aggregates sensor streams to provide real-time asset location updates. The system emphasizes transparent data handling, layered privacy safeguards, and encryption at rest to protect information. Access controls, auditable trails, and data minimization shape governance alongside tracking efficiency. Setup must align capabilities with organizational needs, balancing speed and privacy. Common remediation targets misconfigurations and telemetry gaps, with diagnostics aimed at closing visibility and integration gaps. The effectiveness of these controls prompts questions about practical trade-offs and implementation realism.
What Prism Pulse 4846017041 Does For Real-Time Tracking
Prism Pulse 4846017041 enables real-time tracking by aggregating data from multiple sensors and sources to deliver continuous location updates. The system analyzes streams for accuracy, latency, and fault tolerance, revealing strengths and gaps in coverage.
Prism Pulse emphasizes real time tracking efficiency while highlighting data security and privacy controls, ensuring transparent handling, access limits, and auditable trails for freedom-minded users.
How Prism Pulse Keeps Data Secure And Private
How does Prism Pulse safeguard data throughout the tracking workflow? The system employs layered privacy safeguards and encryption at rest, ensuring data remains unreadable without authorization. Access is narrowly scoped, audits are frequent, and decoupling minimizes linkability. Emphasis on data minimization reduces exposure, while transparent retention policies bolster user trust and support a freedom-forward privacy posture.
Choosing The Right Prism Pulse Setup For Your Needs
Choosing the right Prism Pulse setup hinges on aligning system capabilities with organizational requirements and risk tolerance. The assessment emphasizes prism pulse features, real time tracking, and privacy safeguards, balancing speed with governance. A critical lens clarifies data security implications, vendor scalability, and integration costs, ensuring decisions support freedom while limiting exposure, redundancy, and insider risk through disciplined configuration and ongoing auditing.
Troubleshooting Common Prism Pulse Hiccups And Fixes
Common hiccups in Prism Pulse deployments are typically rooted in misconfigurations, insufficient visibility, or integration gaps, and they warrant a systematic diagnostic approach.
Prism Pulse failures emerge from inconsistent real time tracking data, opaque privacy safeguards, or misaligned setup customization.
Auditors note gaps in telemetry, prompting focused remediation—verify configurations, enhance observability, and validate end-to-end flows to restore trusted, autonomous operation.
Conclusion
Prism Pulse operates like a watchful lighthouse, its beams tracing assets through foggy corridors of data. The system’s real-time fusion of sensor streams mirrors a disciplined navigator, ensuring speed without sacrificing oversight. Yet the harbor remains guarded by strict access docks and encrypted at rest—a reminder that visibility thrives only when governance and minimization dock well. In balancing needs and privacy, misconfigurations are the riptides; with vigilant diagnostics, the voyage stays deliberate and auditable.